ISO 27001 Consultant and Lead Auditor Course Content
This course provides you with the Auditing Skills, the Knowledge of the Standard (including Annex A – Information Security Controls) and the practical application of that knowledge with Audit Scenarios to enable you, as Audit Programme Manager, to undertake and manage Internal Audits for your Organization.
What will I learn from this ISO 27001 Consultant & Lead Auditor Diploma course?
This comprehensive ISO 27001 Consultant and Lead Auditor course is divided into four Modules:
- Module 0: Introduction and background to the Standard and auditing – Explore ISO 27001 and its role in managing information security, showing how consulting and advisory activities support ISMS design, development, and compliance readiness. Understand your consulting perspective in guiding organizations through ISO 27001 requirements and implementation challenges
- Module 1: Auditing Skills based on ISO 19011:2018
-
- Auditing Skills – Develop the ability to plan and conduct ISMS assessments with actionable guidance for ISO 27001 alignment. Review control implementation, verify policies, and recommend improvements
- Terms and definitions – Master ISO 27001 terminology and ISMS-specific language to communicate effectively with clients and stakeholders. Focus on concepts such as control objectives, risk treatment, and information asset management
- Principles of auditing – Apply audit principles to advisory scenarios that enhance ISMS effectiveness. Focus on impartiality, evidence-based evaluation, and confidentiality in information security contexts
- Auditor skills – Enhance analytical, reporting, and advisory skills to improve client ISMS processes. Evaluate control effectiveness, document findings, and coach staff on ISO 27001 compliance
- Managing an audit programme – Organize and oversee ISMS audit programmes for multiple clients or departments. Schedule audits, allocate resources, and monitor progress effectively
- Audit Team Leadership – Lead teams in complex ISMS assessments and mentor inexperienced auditors. Coach for audit readiness and client advisory support
- Overview of Audit activities – Visualize audit stages from planning to follow-up to support clients in ISMS improvement. Tailor audit scopes to organizational risk and compliance priorities.
- Audit activities – Step 1 – Define audit objectives, criteria, and scope in ISMS readiness assessments. Identify critical systems, sensitive data, and key security risks
- Audit activities – Step 2 – Collect and review documentation to assess ISMS policies, procedures, and controls. Evaluate access management, risk registers, and incident response protocols
- Audit activities – Step 3 (2 modules) – Facilitate on-site and remote audit processes to verify ISMS compliance and effectiveness. Conduct personnel interviews and validate controls
- Audit activities – Step 4 – Record findings and communicate gaps or nonconformities in the ISMS. Summarize evidence and recommend corrective or preventive actions
- Audit activities – Step 5 – Evaluate the effectiveness of corrective actions and ISMS controls. Advise on continuous improvement plans to maintain ISO 27001 compliance
- Audit Activities – Step 6 – Prepare final audit reports and follow-up strategies. Present evidence, track risk treatment, and support certification readiness
- FAQs about Auditing – Clarify common challenges in ISMS audits and consulting scenarios. Address audit scope, sampling, and consultant responsibilities
- Online Module Examination – Test knowledge of ISO 27001 audit concepts and the consultant’s role in enhancing information security management systems
- Module 2: Knowledge of the Standard, ISO 27001:2022 – ISMS Requirements
-
- Introduction to ISO 27001:2022 – Understand the ISO 27001 framework and its relevance for developing robust, customized information security systems. Learn the implications of the 2022 revision for information security management
- Terms & Definitions – ISO 27001 – Apply ISO 27001 terminology to communicate clearly with clients on ISMS requirements. Differentiate between risk treatment plans, control objectives, and residual risks
- Fundamentals of Information Security Management Systems (ISMS) – Examine how an ISMS is structured and maintained to protect information assets. Focus on policies, procedures, and operational controls
- ISMS Implementation and Certification to ISO 27001 – the 31 Steps – Follow a structured roadmap to guide organizations from initiation to certification. Cover project scoping, stakeholder engagement, and risk treatment prioritization
- Initiation, Planning, Implementation, and Securing Certification – Guide project setup, risk planning, control implementation, and certification readiness. Align processes with ISO 27001 Annex A and perform gap analyses
- Some Key Aspects of ISMS Auditing – Review ISMS processes and provide actionable guidance while maintaining ISO 27001 compliance. Balance consulting and audit advisory roles
- Structure & Content of ISO 27001:2022 – Analyze ISO 27001 clauses and Annex SL structure to inform ISMS design and implementation. Map information security controls to business processes and risk priorities
- Part 4: Context of the Organization – Identify internal and external factors influencing the ISMS. Evaluate business environment, stakeholder expectations, and regulatory requirements
- Part 5: Leadership – Advise top management on demonstrating ISO 27001 commitment and setting ISMS objectives. Clarify roles, responsibilities, and resource allocation for information security
- Part 6: Planning for the ISMS (2 lessons) – Guide strategic planning for ISO 27001 implementation and risk management. Integrate risk treatment into business processes and align operational priorities with information security goals.
- Information Security Risk Assessment and Treatment – Facilitate client-led risk assessments and actionable treatment plans. Address access management, network protection, and data privacy compliance. Integrate the Annex A IS Controls
- Information Security Objectives and Planning to Achieve Them – Support defining measurable goals to strengthen the ISMS. Set KPIs for incident response, control implementation, and overall security performance
- Part 7: Support (2 lessons) – Establish resources, competencies, and communication strategies to sustain ISMS effectiveness. Implement training programs, document control, and compliance monitoring
- Part 8: Operation – Implement operational controls and processes for day-to-day ISMS management. Manage change, third-party relationships, and security monitoring
- Part 9: Performance Evaluation – Assess ISMS performance and information security effectiveness. Develop dashboards, conduct management reviews, and interpret trends for improvement
- Part 10: Improvement – Integrate continual improvement practices into the ISMS. Take actions to address security incidents and other nonconformities effectively. Update risk treatment plans, enhance controls, and embed lessons learned into operations
- Advanced Aspects of ISMS Auditing (3 lessons) – Support multi-site and complex ISMS implementations. Plan audit readiness, coordinate evidence, and integrate corrective actions
- FAQs about the Standard – Answer common ISMS implementation and certification challenges. Provide guidance for sustaining ISO 27001 compliance
- ISO 27002:2022 – Information Security, Cybersecurity, and Privacy Protection – Implement Annex A Controls to strengthen information security practices. Focus on cryptography, access permissions, and supplier security
- ISO 27006:2015/Amd 1:2020 – Requirements for IS Certification Bodies – Understand certification body operations and align consulting guidance with their expectations
- Online Module Examination – Demonstrate ability to advise clients on ISMS design, ISO 27001 compliance, and information security management
- Module 3: Practice with Scenarios – Apply consulting techniques to real-world ISMS challenges. Handle difficult stakeholders, address nonconformities, and guide certification readiness
- Audit Scenarios – Internal Auditor / Lead Implementer / Lead Auditor – Explore how consultants support different audit roles and adapt guidance for client-specific situations
- FAQs about the Auditing Experience – Incorporate tips for consulting engagements, including aligning ISO 27001 audits with strategic business objectives
What materials are included in this ISO 27001 Lead Implementer Course?
These materials, invaluable when implementing ISO 27001:2022, include:
- ISO 27001:2022 ISMS Implementation Guide (100+ pages)
- Diagram: The 31-step Path to ISO 27001:2022 Certification
- Sample ISMS Policy Manual
- Sample ISMS Maintained Documentation (procedures), including…
- Sample Info Assets, SoA Risk Assessments, and Controls
- Sample Statement of Applicability
- Workbook for Annex A (SoA) Evidence recording
- Sample ISMS Retained Documentation (records)
- ISO 27001:2022 Gap Analysis Tool
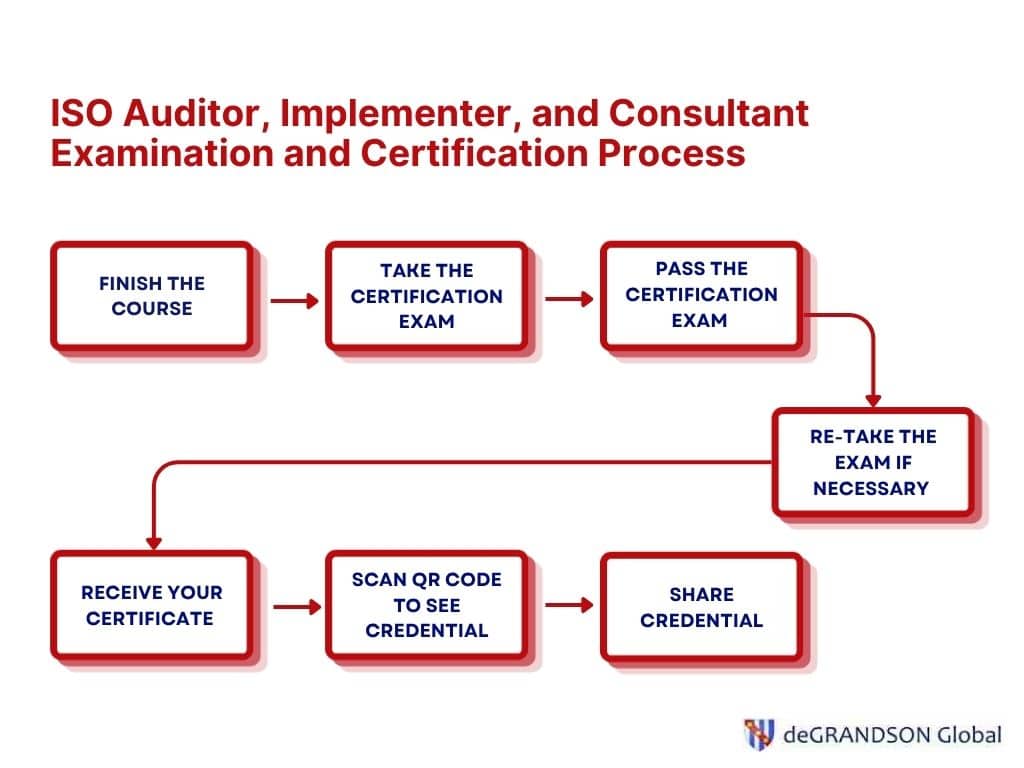
- Diagram: Auditor Certification Process
- Diagram: 6-Stage Audit Process
- Sample Code of Ethics
- Management of an Audit Programme
- Audit Plan example
- Audit Work Order example
- Nonconformity Report example
- EU GDPR Fulltext
- EU GDPR Checklist Templates for SMEs
- Information Security Risk Management process diagram
- Information Security Risk Treatment Activity diagram
- Note: Information Assets
- Information security risk management process
- Information security risk treatment activity
- Chart of ISO 27001 Internal and External COTO Issues
- Sample ISO 27001 FMEA Spreadsheet (Excel file)
- Sample Info Assets, SoA, Risk Assessments, and Controls – combined Spreadsheet (Excel file)
- Sample Statement of Applicability Spreadsheet (Excel file)
- Auditor’s Workbook for Annex A (SoA) Evidence Record (Excel file)
- Stage 1 ISO 27001 Checklist of Critical Issues
- Stage 1 ISO 27001 Lead Auditor Checklist
Who should enroll in this ISO 27001 Consultant & Lead Auditor Diploma course?
This ISO 27001 Consultant and Lead Auditor course is for you:
- If you wish to be an Information Security Management System Consultant.
- If you are Management Representative for your organization and are the Audit Programme Manager for ISMS internal audits.
- If you wish to develop and implement an information security management system for your organization.
- If you are required to perform ISMS internal audits within your organization
- If you are required to perform ISMS supplier audits
- If you wish to improve your career prospects
- If you wish to understand the processes of conducting internal audit or external audits
Key Features:
- Course is accredited to ISO 21001, the standard for Educational Organizations Management Systems
- An ISO 27001 Consultant and Lead Auditor certification is awarded upon passing the certification exam
- Certificate is immediately available online after the successful passing of the exam
- Certificate comes with a shareable QR code for instant verification of credentials
- Lessons range from 15 minutes to 1 hour, typically 20–30 minutes, ensuring that each topic is covered in suitable detail
- Course includes practice with scenarios that include dialogues
- Course includes 24/7 Live-chat Learner Support
- Course includes a learner manual, a copy of the standard, and samples of relevant forms and other documents
- Course comes with full-audio narration and Closed Captions for accessibility
- Courses are hosted on your browser so that no software has to be downloaded avoiding security risks.
- Course comes with quizzes, practice with scenarios, and open-book certification exam
- Course is hosted on your browser so that no software has to be downloaded avoiding security risks.
- Features cross-device compatibility (courses can be taken on any desktop, tablet, or mobile)
- Offers full-resume feature (end a session mid-lesson and continue exactly where you left off, even from a different device)
- Features real-time interactive content in a secure web-based environment
- Offers a clear learning path (once you’ve completed the internal auditor course, you have the option to progress to the lead auditor, up to the consultant and lead auditor course.
- Examination and certificate fee are already included in the course fee
- Payable via PayPal or Stripe using any credit or debit cards
- Option to pay in 4 monthly installments available
Enrollment and Registration Process
To enroll in a deGRANDSON’s ISO auditor course, you would need to go through the following steps:
- Select desired course
- Complete check out proces
- Wait for Payment Confirmation email
- Check your email for the enrollment instructions
- Complete the sign up process
Flexible Payment Options

Pay by Credit Card, Debit Card, SEPA, PayPal Account and more.
Installment Option

Spread the cost of your purchase. Option to pay in 4 monthly installments available for most courses.
Group Discount

Get 10, 15, and 25% discount when you enroll 3, 10, 20 or more people.
About the Course Author

Dr John FitzGerald graduated with a 1st class honours degree in chemistry and a PhD in synthetic organic chemistry. He worked for 15 years in the manufacturing industry, then as a trainer and consultant in the UK and Ireland before founding deGRANDSON Global in 2009.
He serves as the company Director and course developer while occasionally working as a Lead Auditor on ISO 9001, ISO 13485, ISO 14001, ISO 27001, ISO 45001, and ISO 55001 audits for an accredited certification body (CAB).
How is this ISO 27001 Consultant & Lead Auditor Diploma course delivered?
The ISO 27001 Consultant and Lead Auditor Course is delivered online from our Learning Management System (LMS), which is provided and maintained by Inquisiq, the Award-winning Learning Management System. You can explore it at www.degrandsonLMS.com. All Lessons have a full resume and scaling capabilities.
This means, for example, you can:
- Start a Lesson at work on your Work Station running on Windows 10,
- Continue the Lesson on the train home on your iPad running on iOS 9 and,
- Complete the Lesson at home on your Notebook PC running on Windows 8.1.
Are there any prequalifications to enroll in this ISO 27001 Consultant & Lead Auditor Diploma course?
The minimum of a Secondary School Certificate (such as a High School Diploma, Baccalaureate, or similar National Vocational Qualification) combined with 5 years’ work experience, with 2 at managerial/supervisory level, is recommended.
You do not have to provide us with any evidence of your qualifications and experience. However, if you do not meet these requirements, you can expect to struggle with the Course.
Examination and Certification Process
- Finish the ISO 27001 Consultant and Lead Auditor course
- Take the certification exam (the exam is free of charge)
- Pass the certification exam (you have two attempts to pass it)
- Retake the certification exam if necessary
- Receive your certificate in your email within 5 minutes after you’ve successfully completed the certification exam
About your ISO 27001 Consultant and Lead Auditor Certification
After successfully passing the certification exam, you will receive your ISO Auditor certificate providing formal recognition of your achievement.
It comes with features designed to enhance its credibility and make it easier to verify and share your qualification with employers, clients, and your professional network.
These include:
- Your full name
- The type of certificate that was awarded to you
- The issuer of the certificate (deGRANDSON Global)
- Your credential ID number
- The credential signatory (Dr John FitzGerald, Founder and CEO, deGRANDSON Global)
- The date the credential was issued
- A QR code that links to a page where you can share your credential on your social media profiles
About deGRANDSON’s Certification
deGRANDSON’s ISO auditor, implementer, and consultant courses are certified to internationally recognized standards, including ISO 21001:2018 for educational organization management, ISO 29993:2017 for learning services outside formal education, and ISO 29994:2021 for distance learning requirements.
These certifications ensure that the courses are designed, delivered, and assessed according to globally accepted practices for both traditional and online learning environments.
The ISO 21001 certification is issued by Business Quality Assurance International (BQAI), which is accredited by the Irish National Accreditation Board (INAB), a member of international accreditation agreements that support global recognition.
Because of this learners benefit from enhanced credibility with employers and certification bodies, consistent and high-quality course delivery, and greater confidence in the effectiveness and reliability of online learning.

Free ISO 27001 Implementation Handbook
This 90-page instruction manual is free with our ISO 27001 Lead Implementer Course. It is not for sale.
It goes over everything you’ll need to develop, implement, and maintain a management system that can achieve ISO 27001 Certification including the following:
- Initiating the Information Security Management System Project
- Obtain management support (Example of Information Security Policy Statement)
- Assemble Information Security Management System Project Team
- Complete Gap Analysis
- Prepare Information Security Management System Project Plan
- The Information Security Context of the Organisation
- Determine the Information Security Context of the Organisation
- Identify the applicable legal and regulatory requirements
- EU General Data Protection Regulations 2021 (GDPR) (Example of addition of applicable Legislation to Scope of Information Security Management System Statement)
- Determine other interested parties’ needs
- Define and establish an Information Security Management System
- Define the Scope of the Information Security Management System (Example of Scope of Information Security Management System Statement)
- Prepare detailed Information Security Policies (Example of Information Security Policy)
- Define Key Roles and Responsibilities
- The Planning Phase
- Define a method of Risk Assessment
- (Example of CIA Value Table)
- (Example of Table of Contents for Risk Assessment Document)
- Create an inventory of Information Assets to protect (Example of an Inventory of Information Assets)
- Conduct Risk Assessment
- Identify risks (Example of Risk Identification)
- Evaluate the risks (Example of simple Risk Assessment)
- Identify applicable objectives and controls
- Develop Statement of Applicability (Example of Statement of Applicability)
- Develop a Risk Treatment Plan (Examples of Risk Treatment Plan) (Example of Risk Assessment Document with Assessment Information and SOA Included)
- Set up policy and procedures to control risks
- Establish Information Security Management System Objectives and plan to achieve them
- Define a method of Risk Assessment
- Operational Planning and Controls
- Determine the operational planning and control needs
- Identify Monitoring and Measurement Needs (incl. Calibration)
- Establish Operational Controls and Monitoring
- Develop the mandatory and other Documentation required
- The specific requirements for documented information (Example listing of Information Security Management System Policies and Procedures)
- The specific requirements for retained documents
- Determine and secure the required Resources
- Pre-launch Activities
- Deliver Employee Awareness Training
- Establish Internal and External Communications
- Finalise & issue Information Security Management System Documentation
- Complete Job-specific Training (Example of Employee Training Record incl. competency check)
- Go Live! Implement policies, procedures and Information Security objectives plan
- Deploy Policies
- Implement the Risk Treatment Plan and other Procedures
- Control of nonconforming outputs
- Establish Information Security Incident response processes
- Monitor the effectiveness of the Information Security Management System implementation
- Conduct periodic evaluation of performance and effectiveness of Information Security Management System
- Conduct periodic evaluation of fulfilment of compliance requirements
- Periodic re-assessment of Risk Assessments (incl. after major breach or loss of data)
- Periodic re-planning of Risk Treatment Plan and of Improvement Plans
- Conduct periodic Internal Audits
- Conduct periodic Management Reviews
- Implement Continual Improvement (Example of Improvement Plan outline)
- Prepare for a Certification Audit
- Ask for help
- Appendix A: The Path to ISO 27001:2022 Certification – the 31 Steps
- Appendix B: Typical Documentation
- Policies & Procedures
- Records
- Appendix C: Some Sample Procedures, Records and Tools
- Appendix D: Example of Management Review Record

Free ISO 27001 Gap Analysis Tool

Identify systems or process gaps in your management system that can be improved with our ISO 27001 Gap Analysis tool.
Free Lead Auditor Skills Checker

Try any of our ISO courses to assess the adequacy of your lead auditing skills before signing up for a full course.
Free CPD Logbook

Make the most of your ISO Auditor training by tracking your ongoing professional development with a CPD Logbook.
Download your free copy below to record your learning, monitor your progress, and build clear evidence of your continued competence as an auditor.
Free Sample Lesson
Experience the deGRANDSON e-Training Method for yourself – user-friendly and intuitive – with one of these Free Sample Lesson.
Choose between:
- Option 1: The 5-minute Sample Lesson
- Option 2: The 30-minute Free Sample Lesson
Newsletter Subscription
Get updates on the latest news about ISO management systems or the latest promotional offers. Subscribe for a 10% discount.